Encryption and password protection are two different methods or techniques to protect your information or data from attackers.
There are many types and sub-divisions with encryption and password protection. Both techniques are used since ancient times.
Primarily they are used to secure sensitive information.
Key Takeaways
- Encryption scrambles data, making it unreadable without the correct decryption key, while password protection restricts access to authorized users.
- Encryption provides a higher level of security than password protection alone.
- Both methods protect sensitive information, but encryption offers more robust protection against data breaches.
Encryption vs Password Protection
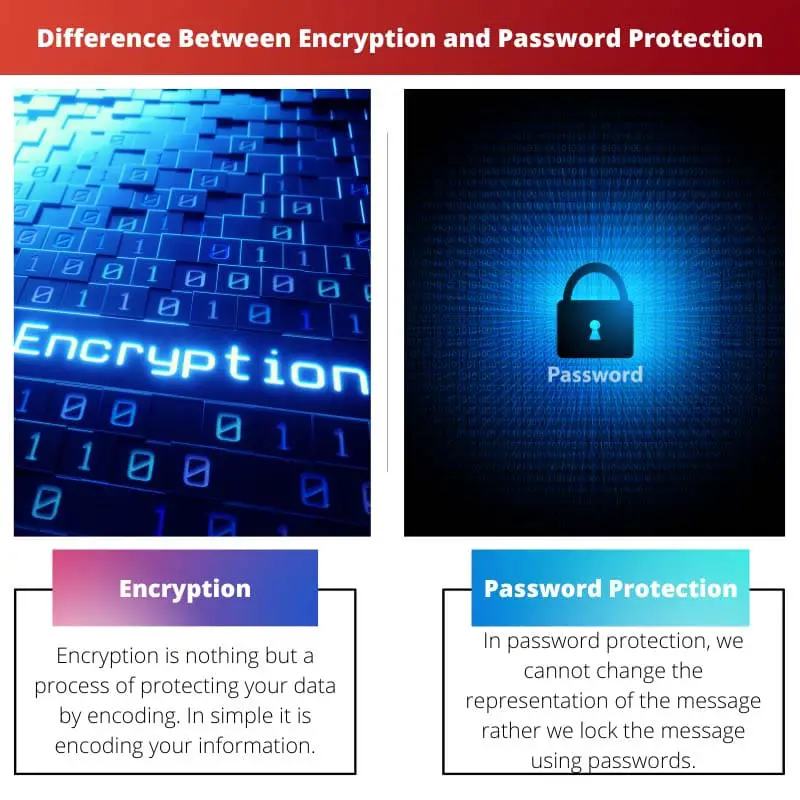
Encryption is the process of encoding information or data in such a way that it can only be read by those with authorized access to the key. Password protection is a security measure that involves requiring a password to access a system or device, helping prevent unauthorized access.

Encryption is nothing but a process of protecting your data by encoding. In simple it is encoding your information.
In encryption, we convert the message or information or plaintext into ciphertext. The ciphertext is nothing but the encoded message.
A key is used for the encryption of the message. Using the key, the encryption is divided into two different types.
The encryption of text will completely change the original representation of the message. Without the key used for the encryption, the message cannot be decrypted.
This method is used in the early days to pass information.
Password protection is quite different from the encryption concept. In password protection, we cannot change the representation of the message rather we lock the message using passwords.
By setting the password, another user cannot open your files and steal your data. The password must be a powerful and difficult find.
Most of the applications and websites ask you for a strong eight-letter password before signing in. You need to be careful before using your personal information as a password.
It must be avoided.
Comparison Table
| Parameters of comparison | Encryption | Password protection |
|---|---|---|
| Types | Encryption has two types | Password protection has no types |
| First used | Encryption is first used in Ancient Greece and Rome | Password protection is first used in Rome Military |
| Needed | Key is needed for encryption | A passcode is needed for password protection |
| Layer | Encryption has multi-layers to break the algorithm | The passcode has a single layer to crack the passcodes |
| Example | Caesar cipher | Hsd90oi@ |
What is Encryption?
Encryption is a process of encoding information for securing the confidentiality of sensitive information. The two vital things needed for encryption are plaintext and key.
Encryption is used as a pseudo-random generator for several technical reasons. In several cases, the message can be decrypted without passing the key using high computational skills.
In cryptography, various forms of encryption are used to send information. Encryption plays a vital role in military and modern computing.
Symmetric key and Asymmetric key are the two types of encryptions.
In symmetric-key encryption, the public key is used. Only one key called the public key is used, which is known to both the sender and the receiver.
In asymmetric encryption, private and public keys are used. Here, the public key is known to both the sender and receiver, whereas the private key is unknown or separate private keys used for sender and receiver.
Encryption provides privacy, data integrity, security, authentication, and regulations. The AES and Triple DES are typical symmetric key encryption.
The RSA and elliptic curve cryptography are common asymmetric encryption. Brute force is the standard type of attack used by the attacker to break the encryption when they know the keys.
Encryption provides a high range of security to your data.

What is Password Protection?
Passwords are like keys. A strong password is equal to a strong door.
The attacker uses various techniques to break your password. In this modern world, it is easy to find passwords when it is easy.
Brute force attacks and many other attacks can easily find the passwords of the user. In organizations, password protection policies are needed to be introduced.
It will help the newbies to know about the importance of passwords and the methods of creating strong passwords.
Password protection is nothing but the implementation of a lock to your computer, mobile phones, and many other gadgets. Sometimes we don’t want to share our gadgets with anyone, and we put passwords.
Even you need to provide a password before logging into your computer. If the password is not strong and easy to find, anyone can access your computer and steal your information.
The forget password option is provided by default.
The passcode is the other name of the password. Since ancient times passcodes are used to protect highly sensitive information.
You don’t use a similar password to all the devices and websites you logged instantly. If one of your passwords is leaked, the attacker can hack all your devices easily.
And he steals your data. Your data will earn money for them.
Information stealing is more familiar nowadays.

Main Differences Between Encryption and Password Protection
- The data has been hidden using algorithms in encryption, whereas passwords are used to hide the data in password protection.
- In encryption key is used, whereas in passwords combination of special characters is used.
- When compared to encryption, passwords are less securable.
- Encryption can change the message into unreadable, whereas password protection cannot change the message.
- When compared to encryption, passwords are easily hacked by malware.
- https://ieeexplore.ieee.org/abstract/document/1089771/
- https://dl.acm.org/doi/abs/10.1145/359168.359172
